Abstract
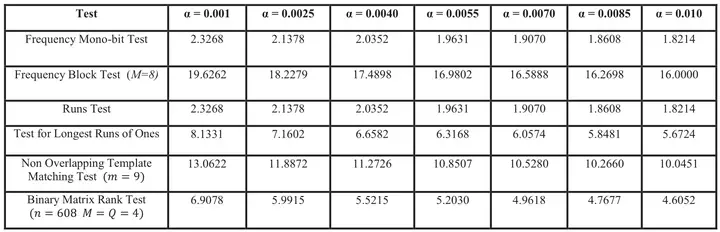
On-chip Random Number Generators (RNGs) are critical components in lightweight ubiquitous devices like RFIDs and smart cards. These devices require low cost test methodologies and security against cryptanalytic and invasive attacks. In this work we propose an on-chip implementation of a reduced set of NIST-SP-800-22 randomness test suite to provide on-line RNG testing for low cost security devices along with runtime monitoring of RNG performance. The on-chip NIST module monitors the effect of dynamic variation of operating condition and time dependent wear-out on RNG circuits. It indicates invasive attacks on RNG and allows the secure system to take protective measures. Six NIST tests are optimized to a hardware design friendly format, but in compliance with the NIST standard. The lightweight implementations reduce complex statistical and arithmetic operations of conventional NIST tests to a series of bit stream count and compare operations. A cycle-to-cycle serial test of incoming bits from RNG eliminates need for additional storage. A partial re-configurable feature is designed to set the pass/fail threshold for each test depending on the system requirements. The on-chip NIST module, although not exhaustive, is an effective layer of validation and security for RNG circuits. The six 128-bit tests implemented in 45nm NCSU PDK have a total synthesized area of ~1926.sq.um for an optimized frequency of 2GHz. The total dynamic power is 3.75mW and leakage power is 10.5μW. At 2Gbps, the NIST module consumes 1.87pJ/bit. The lightweight ultra-low power implementation is scalable for larger input bit samples.