BLERP: BLE Re-Pairing Attacks and Defenses
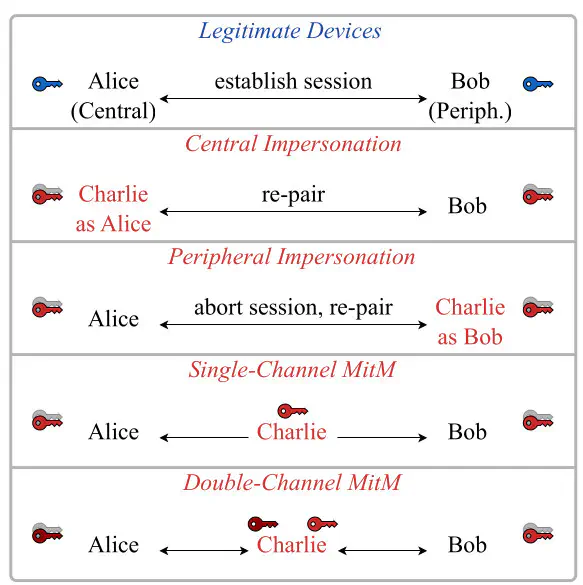
In mid 2024, Tom and I looked at BLE re-pairing, an underlooked attack surface. We uncovered four critical re-pairing attacks and design-level vulnerabilities that allow device impersonation and MitM of arbitrary devices in BLE range. The attacks work even in the most secure BLE modes, like authenticated pairing and Secure Connections Only, and require 0-click or 1-click interactions.
As part of our responsible disclosure we also proposed effective countermeasures that can be adopted by implementers and by the Bluetooth SIG. AFAIK, the Bluetooth SIG is not planning to fix the BLERP attacks and vulnerabilities, although they should.
After almost 1.5 years, we publicly release the BLERP paper and codebase: